TPRM manages supplier and vendor risks, whilst FPRM manages risks within your own systems, people, and processes. CISOs and SOC leaders often treat vendor risk as “the same controls, just external.” That assumption breaks fast. In TPRM third party risk management, the security boundary is outside your administrative control. You rely on contracts, attestations, and telemetry you can negotiate. In first party risk management (FPRM), you own the environment, the control design, and the evidence. This difference changes how you prioritize remediation, measure assurance, and handle incidents.
Modern frameworks increasingly push organizations to manage risk across the full ecosystem, not only internally. NIST CSF 2.0 adds a dedicated GOVERN function to tie cybersecurity risk decisions to enterprise governance and stakeholder expectations. NIST’s supply chain guidance (C-SCRM) explicitly treats suppliers, products, and service providers as a distinct risk surface requiring specialized practices. Regulators also codify this distinction: the EU’s DORA regime, for example, includes specific expectations for ICT third-party risk in financial services.
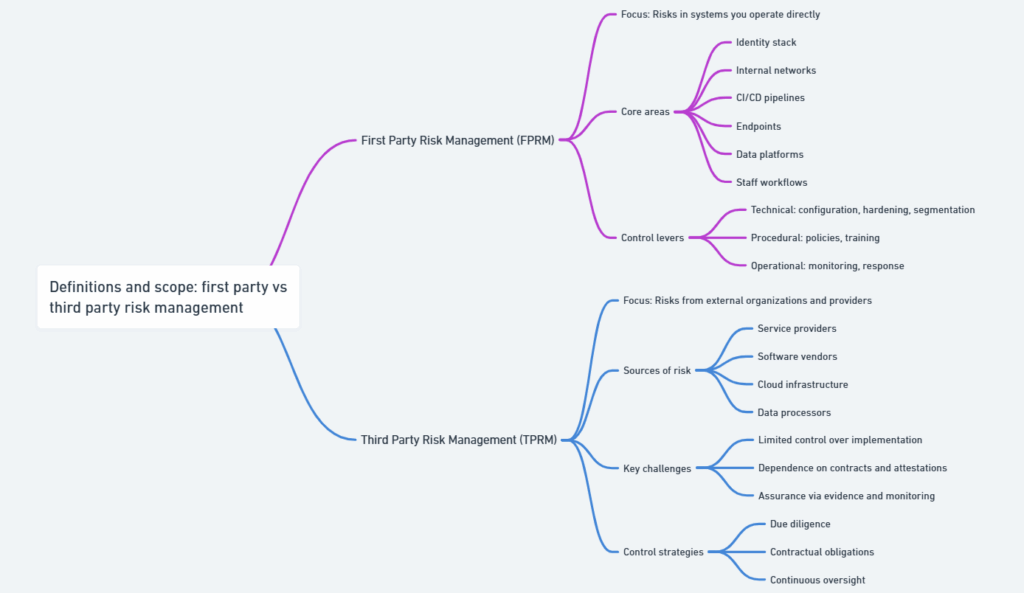
Definitions and scope: what “first party” and “third party” mean in practice
First party risk management (FPRM) is how you identify, measure, treat, and monitor risks in systems and processes you operate and can directly change. That includes your identity stack, internal networks, CI/CD, endpoints, data platforms, and your own staff workflows. Your levers are technical (configuration, hardening, segmentation), procedural (policy, training), and operational (monitoring, response).
Third party risk management (TPRM) covers risks introduced by external organizations that provide services, software, infrastructure, or access to your data and operations. The third party might host workloads, process regulated data, supply software components, or connect into your environment. NIST’s control catalog explicitly distinguishes “external system services,” noting you have no direct control over how required controls are implemented or assessed. That single sentence explains why TPRM often needs different assurance mechanics than FPRM.
Ownership boundaries: accountability, control, and assurance differences
The cleanest way to separate TPRM vs FPRM is by answering three questions:
- Who can implement or change the control? (You in FPRM; the supplier in TPRM.)
- Who can generate trustworthy evidence at the source? (You can instrument internally; externally you depend on what’s shared.)
- Who bears contractual or regulatory responsibility for outcomes? (Often shared; frequently asymmetric when data or customer impact is yours.)
This is why “same policy, different scope” fails. In FPRM, you can mandate MFA, rotate secrets, or block egress today. In TPRM, you may only be able to require those outcomes via contract language, audit rights, and service-level commitments—then verify them through attestations or technical signals.
Comparison matrix: differences between third party risk management and first party risk management
Security leaders frequently ask for a single artifact that helps align procurement, legal, IT, and SecOps. The matrix below frames the Differences between third party risk management and first party risk management as a set of operating assumptions.
| Dimension | FPRM (first party) | TPRM (third party) | Practical implication |
|---|---|---|---|
| Control authority | Direct administrative control | Indirect, via contract + relationship | Escalation and timelines differ |
| Evidence quality | Telemetry + internal audits + testing | Reports, attestations, limited telemetry | Assurance is often probabilistic |
| Monitoring cadence | Continuous by default | Periodic + event-driven | You must detect “silent changes” |
| Enforcement levers | Config, policy, disciplinary action | Contract terms, renewals, penalties | Remediation depends on leverage |
| Incident response | Full runbooks and tooling access | Coordination + notification clauses | MTTR depends on supplier readiness |
| Scope boundaries | Your assets and people | Supplier + sub-processors + fourth parties | Dependency mapping is mandatory |
| Residual risk | Usually reducible via engineering | Often accepted or compensated | Risk acceptance is more common |
| Audit posture | You can produce primary evidence | You aggregate supplier evidence | Audit-readiness requires curation |
Framework mapping helps keep this disciplined. ISO/IEC 27002:2022 explicitly names supplier-focused controls (5.19–5.21) and points to the ISO/IEC 27036 series for supplier relationships.
Risk and control domains that diverge between TPRM and FPRM
Many risk domains exist in both models, but they behave differently once the boundary is external.
Key domains where TPRM needs distinct treatment:
- Identity and access delegation: federated SSO, privileged access at the supplier, and support channels
- Data handling and sub-processing: storage locations, encryption, retention, and downstream processors
- Software supply chain exposure: dependencies, build integrity, update channels, and vulnerability response
- Resilience and concentration risk: shared cloud regions, common providers, and correlated outages
- Assurance and audit rights: what you can verify vs what you must trust
The core pattern: in TPRM, your strongest controls are often selection, contracting, and verification, not configuration.
Lifecycle workflows: how TPRM and FPRM run end-to-end
Operationally, both programs follow a lifecycle. What changes is who performs each step, and what evidence is credible.
Intake and due diligence: vendor onboarding vs internal asset onboarding
FPRM onboarding is about architecture review, threat modeling, and control implementation before go-live. TPRM onboarding is about defining required outcomes and then validating supplier posture.
Minimum evidence set that scales across vendors:
- Current security attestations (e.g., SOC 2 scope + period) and/or ISO certifications
- Data flow description: what data, where processed, and who can access it
- Incident notification commitments, RTO/RPO expectations, and contact paths
- Sub-processor list (where applicable) and change notification terms
SOC 2 relies on the AICPA Trust Services Criteria, which define control criteria used to evaluate controls relevant to security and related categories.
Continuous monitoring: control drift, changes, and incident signals
FPRM continuous monitoring is largely telemetry-driven: configuration drift, endpoint health, detection coverage, and vulnerability trends. TPRM monitoring is a hybrid of:
- Periodic reassessment: annual or semiannual review of reports, scope changes, and control exceptions
- Event-driven triggers: ownership changes, major platform migrations, breaches, new sub-processors
- Technical signals: reachable endpoints, certificate hygiene, vulnerability disclosures, and security advisories
NIST treats external services as outside your authorization boundary, which is why “continuous” in TPRM often means “continuous triggers,” not continuous internal telemetry.
Exit management: termination, data return, and residual risk
TPRM offboarding is a risk event. The goal is to prevent data persistence and access persistence.
Offboarding requirements to institutionalize:
- Data return or verified deletion, including backups and replicas
- Credential and federation teardown (SSO, API keys, service accounts)
- Revocation of support access paths and ticketing links
- Post-termination breach notification coverage (for late-discovered incidents)
In regulated processing contexts, contracts often must specify processor obligations and security measures—reinforcing why exit clauses are a security control, not just legal language.
Evidence and assessment methods for scalable assurance
Scaling assurance means matching assessment depth to criticality, not treating every vendor the same.
Structured evidence: questionnaires, attestations, and control mappings
Structured evidence is fast, comparable, and audit-friendly, but it is also easier to game.
Quality rules that reduce false confidence:
- Prefer Type II style operating-effectiveness periods over point-in-time snapshots
- Validate scope: system boundaries, excluded services, and carve-outs
- Require disclosure of material subservice providers and shared components
- Map evidence to your control objectives, not to the vendor’s marketing language
ISO’s supplier controls (27002:2022 5.19–5.21) provide a useful structure for this mapping, especially when suppliers claim alignment.
Technical validation: telemetry, scans, SBOMs, and testing artifacts
Technical validation complements paperwork when risk is high or when exposure is direct (network connectivity, sensitive data, or operational dependency). Practical options:
- External attack surface discovery and continuous exposure monitoring
- Secure configuration validation for tenant-controlled settings (cloud SaaS knobs)
- Vulnerability disclosure and patch SLAs with proof of execution
- Pen test summaries and remediation evidence for in-scope components
- Software supply chain artifacts (e.g., dependency inventory) when you integrate code
NIST’s supply chain guidance is explicit that acquirers and end users need practices that cover acquired products and services, not only internally developed systems.
Tooling and automation: connecting GRC, IAM, SecOps, and procurement
TPRM fails when it is a document workflow disconnected from operations. FPRM fails when controls are engineered but not governed. Mature programs integrate:
- Procurement intake → risk tiering (criticality, data types, connectivity)
- IAM → least privilege (SCIM/SSO enforcement, just-in-time access, PAM paths)
- SecOps → detection + response alignment (shared playbooks, notification SLAs)
- GRC → evidence and exception tracking (time-bounded exceptions, compensating controls)
Automation opportunities that typically produce immediate value:
- Auto-classify vendors based on data categories and integration type
- Trigger reassessment on material changes (renewal, scope expansion, acquisitions)
- Pull standardized evidence metadata (report period, scope, carve-outs) into your GRC
This supports “operational TPRM,” where the SOC sees vendor exposure as part of the detection surface.
Metrics that matter: KRIs and KPIs for CISOs, CIOs, and SOC managers
Metrics should show exposure, assurance, and response readiness, without rewarding checkbox behavior.
TPRM third party risk management metrics that predict exposure
| Metric (KPI/KRI) | What it indicates |
|---|---|
| % critical vendors with current assurance evidence | Coverage of your highest dependency risks |
| Median time to close vendor high findings | Supplier remediation velocity |
| # vendors with high-risk sub-processors (unreviewed) | Fourth-party amplification |
| % vendors meeting incident notification SLA | IR coordination readiness |
In sectors impacted by regimes like DORA, third-party posture is not optional program maturity—it is a compliance vector.
FPRM metrics that improve internal control reliability
| Metric (KPI/KRI) | What it indicates |
|---|---|
| % privileged access protected by phishing-resistant MFA | Control strength on critical paths |
| Mean time to remediate critical vulns by asset class | Engineering throughput and risk burn-down |
| Detection coverage for crown jewels (log sources + rules) | SOC visibility into high-impact assets |
| Backup restore test success rate | Resilience, not just backup existence |
NIST CSF 2.0’s GOVERN focus supports tying these metrics to decision-making and accountability, not only to technical operations.
Standards and regulatory expectations: aligning TPRM vs FPRM controls
A practical way to satisfy auditors and regulators is to treat standards as control objective libraries, then implement them differently by boundary.
- NIST SP 800-53 Rev. 5 includes supply chain risk management as a dedicated control family (SR), reinforcing that supplier risk is a first-class control domain.
- ISO/IEC 27002:2022 names supplier-focused controls (5.19–5.21) and the ISO/IEC 27036 series frames supplier relationship security from both acquirer and supplier perspectives.
- NIS2 establishes cybersecurity risk-management measures at EU level and explicitly includes supply chain dimensions in its risk framing.
- SEC cybersecurity disclosures increase pressure to understand and govern cyber risk, including when incidents involve third-party systems, because material incidents and risk management practices must be disclosed.
The design lesson: pick a control objective (e.g., “access control”), then define two implementations—one for internal systems and one for supplier environments—each with its own evidence model.
Operating model design: roles, escalation, and exception handling
Programs scale when decision rights are explicit. TPRM usually needs more non-security stakeholders than FPRM because your leverage is often contractual and commercial.
RACI across security, IT, legal, privacy, and vendor management
Sample RACI slice (adapt to your org structure):
| Activity | Security | IT/Architecture | Procurement | Legal | Privacy | Business Owner |
|---|---|---|---|---|---|---|
| Risk tiering | A/R | C | C | C | C | R |
| Security requirements | A/R | C | C | C | C | C |
| Contract security clauses | C | C | C | A/R | C | C |
| DPIA / processor terms | C | C | I | C | A/R | C |
| Go-live decision | A | A/R | C | C | C | A/R |
| Exception approval | A/R | C | I | C | C | A |
GDPR/UK GDPR contracting expectations illustrate why privacy must be part of TPRM when personal data is processed, including required security obligations in processor contracts.
Risk acceptance: compensating controls and contractual levers
In FPRM, exceptions are often engineering debt. In TPRM, exceptions are often negotiation outcomes. Keep acceptance disciplined:
- Time-bound exceptions with explicit renewal gates
- Compensating controls you can enforce (segmentation, reduced scope, tokenization)
- Contractual levers (right to audit, breach notification timelines, termination rights)
- Clear “no-go” criteria for critical risks (e.g., unmanaged privileged access)
This is where TPRM vs FPRM becomes a governance topic, not only a security topic.
Common failure modes in TPRM vs FPRM (and how to prevent them)
Most failures are predictable patterns in boundary management.
Failure modes to actively design against:
- Scope drift: vendor adds services or regions; your assessment scope stays static
- Paper assurance: reports exist but exclude the service you actually use
- Fourth-party blindness: sub-processors are unknown or change without notice
- Access creep: support access remains after projects end
- Non-operational IR: notification clauses exist, but no joint runbooks or contacts
- One-size questionnaires: critical vendors and low-risk tools get identical treatment
- Undefined risk ownership: business owners assume security “approved” the vendor
Prevention is mostly workflow design: tiering, triggers, scope validation, and enforcement of offboarding.
Implementation checklist: building a unified, audit-ready program
Use this as a build sequence that avoids premature tooling complexity.
- Establish a vendor taxonomy (data type, connectivity, criticality, concentration)
- Define tier-specific control objectives and required evidence
- Standardize security contract clauses (notification, audit rights, sub-processors, exit)
- Implement intake gating: no integration before tiering + minimum evidence
- Connect IAM controls: SSO required, least privilege, scoped API keys, periodic reviews
- Add continuous triggers: renewals, acquisitions, major product changes, new regions
- Create SOC-ready vendor playbooks: contacts, escalation paths, evidence locations
- Measure what you manage: coverage, remediation time, notification compliance, exceptions
Standards can be your alignment backbone: NIST CSF 2.0 for governance framing, NIST 800-53 for control objectives, and ISO supplier controls for structured supplier coverage.
Closing guidance: when to converge controls and when to separate
Converge control objectives across TPRM and FPRM (e.g., access control, logging, resilience) so leadership can reason about risk consistently. Separate implementation and evidence because ownership differs. For first-party systems, favor instrumentation, hard controls, and continuous validation. For third parties, favor tiered requirements, strong contracting, scope-aware assurance, and event-driven monitoring.
If you want a concise executive phrase for steering committees: FPRM is engineering-led risk reduction; TPRM is governance-led risk containment. That framing helps keep the program honest, keeps the SOC informed, and keeps procurement aligned—without pretending that an external provider can be managed like an internal system.








