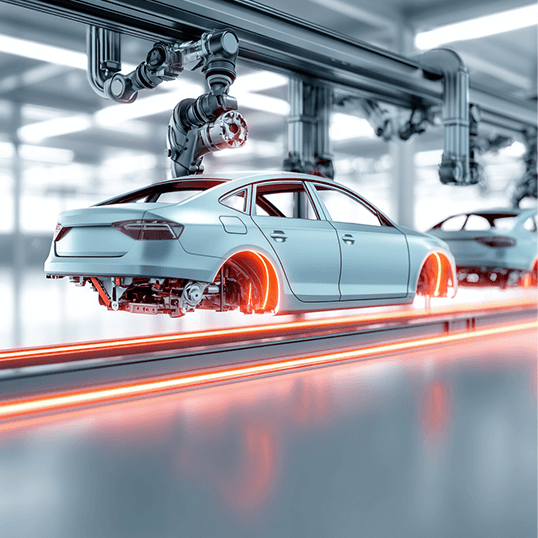
Automotive
Securing the future of mobility
With the rapid advancement of technology in the automotive industry, vehicles have become complex, interconnected systems – creating new opportunities for unprecedented mobility and convenience. At the same time, the numerous communication interfaces in modern vehicles introduce vulnerabilities that can be exploited by cybercriminals. Weaknesses in connected systems – including WiFi, Bluetooth, cellular networks, and telematics systems – can be exploited to give threat actors unauthorized access, manipulate vehicle controls, steal sensitive data, or even exert control of an entire vehicle.

Recognized as industry leaders
Paving the way to a secure future in the automotive industry
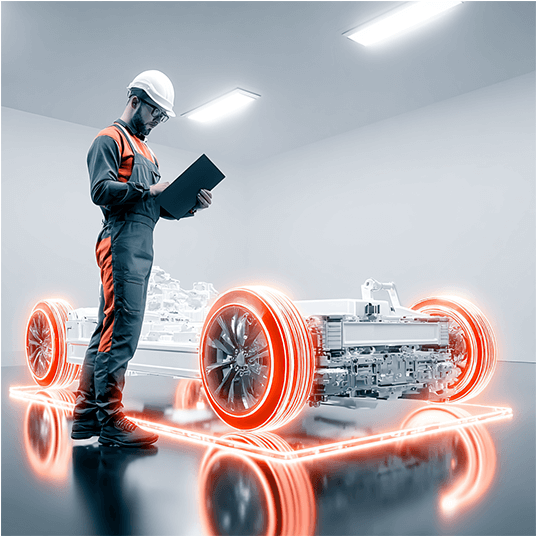
The automotive industry relies heavily on software and firmware to power various vehicle systems, including infotainment, engine control units (ECUs), advanced driver-assistance systems (ADAS), and autonomous driving capabilities. Vulnerabilities in software and firmware can lead to problems ranging from system malfunctions and unauthorized control of critical functions to potential accidents. Moreover, with enterprises working with multiple suppliers and vendors, malicious actors aim to compromise the integrity of components and inject malware into software updates or infiltrate weak links in the supply chain. Robust security strategies are essential to ensure the safety, security, and trustworthiness of vehicles now and in the future.

Ensuring vehicle and passenger safety

Cloud-native & hybrid deployment
providing greater operational efficiency, with cloud-native tools and automations accelerating detection & response
Reduced time to respond
with orchestration and automation capabilities that provide faster time to response and increased threat landscape visibility

Single view of operations
supporting multi-team SecOps collaboration, with real-time alerts and recommendations for security incidents
Fewer false positives
data and logs are collected from multiple sources, enriching alerts by providing additional context, while reducing errors and time to detect
Leveraging automation to mitigate risk
In an era in which enterprises must maintain multi-cloud environments, automation serves as a critical component – reducing risk while improving efficiency and scalability. Our eBook on “How to leverage automation to mitigate risk” explores the essential components of secure cloud transformation, and how automation can support an efficient and scalable move to the cloud.
Best practices in handling real threat scenarios
SOC L1 and L2, DFIR, Threat Intel, and Threat Hunter teams collaborate to mitigate threats faster and more effectively. Our Cyber Defenders Playbook reviews “lessons learned” by CyberProof’s team to help you improve your detection & response processes.
Improving cyber resilience by leveraging the MITRE ATT&CK
MITRE’s Attacker Tactics, Techniques, and Common Knowledge (ATT&CK) framework is a powerful tool for improving cyber defense. MITRE creates a categorized list of all known attack methods, and connects each attack method with mitigations and detection methods for preventing or identifying attacker techniques.

Migrating to the cloud and adopting Microsoft Azure Sentinel to improve security resilience
READ MORE
Further Resources

Travel
The client chose CyberProof to provide advanced Managed Detection & Response (MDR) services including 24×7 L1 & L2 SOC services and platform management services – utilizing Microsoft Sentinel, Splunk, XSOAR, CrowdStrike and Cortex XDR security technologies. The client also uses CyberProof’s Use Case Management Service to manage existing use cases and develop new ones.

Aviation
The client is one of the world’s top airlines. It operates flights serving over eighty international destinations in more than thirty countries. The airline must ensure round-the-clock safety and security for all its operations. The client’s IT ecosystem includes a combination of on-premises and cloud architecture, e-commerce, third-party hosting, application access and management, endpoints, and more.
Speak with an expert
Discover how we can help you ensure the safety of vehicles by implementing robust data protection measures to identify and mitigate cyber threats.