IDENTIFYING GAPS AND PREEMPTING ATTACKS
Penetration Testing
Proactively identify vulnerabilities to manage cyber risk while reducing business impact
RECOGNIZED AS INDUSTRY LEADERS
Thwart the hacker by embodying the hacker
Pen Testing Services
CyberProof’s penetration testing services offer a comprehensive set of capabilities to proactively detect and validate vulnerabilities, configuration weaknesses, control gaps, and staff awareness within organizations by safely performing the actions a malicious actor would.
We help organizations better understand the evolving threat landscape and manage cyber risks to keep their systems secure with these services:
- Application Penetration Testing Services
- Network Penetration Testing Services
- Mobile Application Penetration Testing Services
- IoT and OT Testing Services
- Red Team Simulation Testing Services

The threat to enterprises
In the current cybersecurity landscape, organizations face a multitude of sophisticated and multifaceted threats that require equally advanced and multifaceted solutions.
Data breaches, which involve unauthorized access to sensitive databases and networks, pose a significant threat to businesses, while phishing attacks, malware infections, DDoS attacks, and ransomware attacks remain common threats.
These threats have become increasingly complex, with attackers using a range of tactics and techniques to compromise systems and steal sensitive data.
Keeping pace with change
While the need for pen testing originated with regulatory requirements, the primary motivations for pen testing today are security validation, potential damage assessment, and cyber insurance.
Most enterprise IT environments are updated more frequently than in the past, with assets being added or removed every few months, or weeks, requiring the security of those environments and attack surfaces to be assessed at a faster testing cadence.
When the validation rate is lower than the change rate, IT infrastructures remain untested for long periods of time, putting the business at risk.
Penetration testing to identify and remediate risk
Penetration testing is a crucial for organizations to identify and address application and network vulnerabilities before they can be exploited.
By simulating real-world attacks, pen testing uncovers security weaknesses that could be exploited by malicious actors, enabling proactive measures to improve overall security posture.
This helps to estimate any damage, understand emerging threats and vulnerabilities, comply with regulations, and develop a comprehensive cybersecurity strategy aligned with business objectives.

Our penetration testing approach
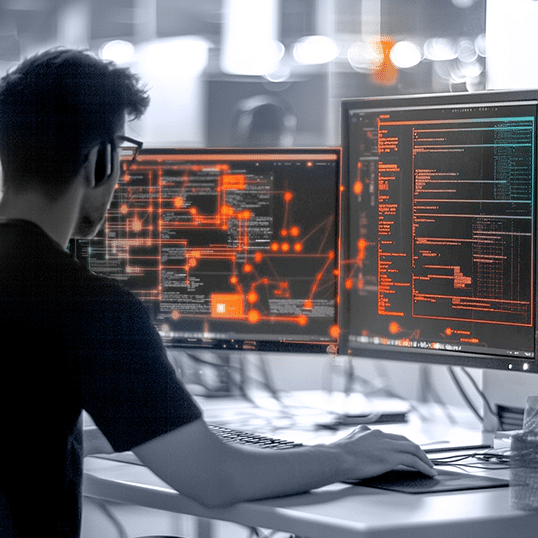
At CyberProof, we understand the complexities of the modern threat landscape that enterprises face. We conduct penetration testing to identify and address specific threats, such as data breaches, phishing attacks, malware infections, DDoS attacks, and ransomware attacks.
Our ethical hackers use a systematic technical approach to search for and find security loopholes in your network or software systems. We then perform penetration testing to explore and exploit these vulnerabilities, confirming their existence and estimating the possible damage to your applications or networks.
Our approach is designed to enable enterprises to proactively counteract against evolving and specific cyber threats, providing comprehensive protection against potential attacks.
What you can expect

Expert Ethical Hackers
A team of experienced ethical hackers that understands the mindset of malicious attackers, employs the same tactics, techniques, and procedures to expose vulnerabilities.

Real-World Attack Simulations
Simulations of real-world attacks are performed on your applications and networks, enabling us to assess your system’s resilience effectively.
Comprehensive Reports
A detailed report is provided after each penetration test, outlining the vulnerabilities found, the risks they pose, and the recommended mitigation steps.

Continuous Improvement
Ongoing testing and support ensure that your applications remain secure as new threats emerge, and your business evolves.
Understanding the value
- Robust Security: By understanding and addressing your system’s vulnerabilities, you can protect your applications from potential cyberattacks, ensuring robust security.
- Informed Decision-Making: Real-world attack simulations and detailed reports enable you to make informed decisions about your security strategy, prioritizing resources where they’re most needed.
- Compliance and Trust: By effectively addressing vulnerabilities, you can demonstrate your commitment to security, ensuring compliance with industry standards and solidifying trust with your customers and stakeholders.
- Future-Proof Business: With ongoing support and continuous improvement, you can stay ahead of emerging threats, safeguarding your organization’s security and resilience in the face of future challenges.
Speak with an expert
Discover how we can help you to identify and address application and network vulnerabilities before they can be exploited.