
Case Study – Travel
Reducing exposure and improving MTTR for a global provider of travel and leisure software services with 24×7 MDR
DOWNLOAD THE PDFAbout the client
The client is a leading provider of travel and leisure software solutions that supports airlines, hotels, and agencies worldwide. Operating at global scale with millions of daily transactions, the organization required advanced cybersecurity capabilities to safeguard sensitive customer and partner data and strengthen threat detection.
The client’s challenge
The client faced multiple challenges as it migrated core applications to the cloud. Their incumbent provider operated as a “black box,” limiting visibility into exposures and slowing detection. At the same time, fragmented processes across a complex technology stack left gaps in monitoring and compliance.
The client needed a strategic partner in Microsoft Azure to implement a cloud-native SOC with 24×7 coverage, transparent operations, and a sustainable (UCM) framework — ensuring detection kept pace with evolving threats targeting the travel sector.
Benefits
- Extended visibility: 9TB/day of data ingestion across 60,000 endpoints
- Faster response: 24×7 MDR operations reduced exposure windows and MTTR
- Sustainable detection: Continuous Use Case Management aligned defenses to evolving threats
- Cloud-native resilience: Smooth migration from legacy SIEM to Microsoft Sentinel

Our solution
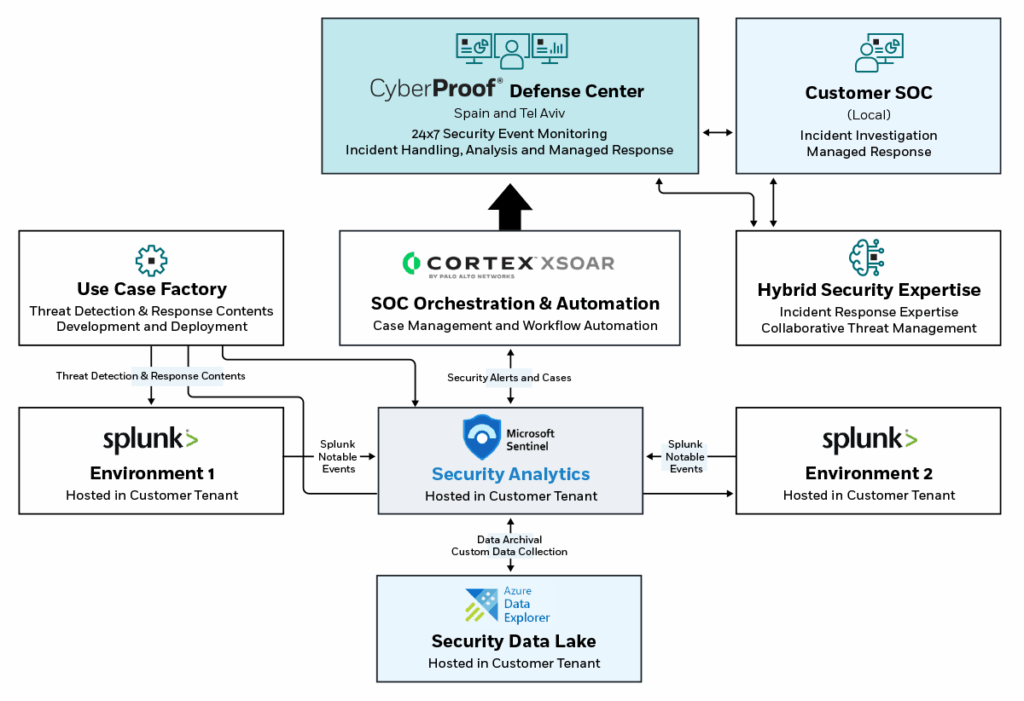
CyberProof deployed a solution in two phases. First, assistance with setting up Microsoft Sentinel SIEM and building a cloud data lake, and next, taking over the 24×7 security operations service.
In stage one, CyberProof integrated both native and non-native sources, ingesting over 9TB/day of data across 60,000 endpoints, and developed tailored detection rules and playbooks.
The service then extended to 24×7 L1 and L2 SOC operations, leveraging Microsoft Sentinel, Splunk, Cortex XDR, CrowdStrike, and XSOAR, supported by CyberProof’s UCM to continuously update, test, and deploy new detections aligned to evolving threats. A hybrid model provided transparent visibility and allowed the client to retain control, while CyberProof experts managed day-to-day operations.
Results
The engagement delivered faster, threat-informed detection and response while enabling a smooth migration from legacy to cloud-native security. The client achieved extended monitoring across new cloud services, a sustainable Use Case Management and governance program, and direct access to highly skilled Microsoft-certified professionals. The outcome was improved resilience, reduced exposure, and greater confidence in securing critical travel and leisure systems against adversaries.
Speak with an expert
Explore how CyberProof can help you anticipate, prevent, and mitigate ever-evolving cyberattacks in hybrid and cloud-native environments.







