When Gartner introduced Continuous Threat Exposure Management (CTEM), it signaled a fundamental shift in cybersecurity, moving from reactive defense to continuous, threat-led risk reduction.
But for many organizations, CTEM remains more of an aspiration than an operational reality.
According to Nick Lantuh, CEO and co-founder of Interpres Security™ (and since Interpres’s acquisition by CyberProof in December 2024, now President of Interpres Group at CyberProof), the issue is not a lack of tools and data, but a lack of connection between them. As he explains, “most organizations have invested in all the right tools, from attack surface management, cloud security, vulnerability management, threat intelligence, etc., but they still struggle to gain a holistic view providing a cohesive, operational threat-led model.”
The missing layer in CTEM
Modern security environments generate vast amounts of data across EDR, SIEM, vulnerability management, XDR, and cloud security platforms. Yet that data often remains siloed and fragmented.
Nick highlights the core problem clearly: “the challenge is not collecting data, it is making sense of it. Without unifying and contextualizing these data sources, organizations cannot clearly see where their gaps and misconfigurations are or what to prioritize.”
This fragmentation leads to blind spots, slows decision-making, and ultimately prevents organizations from acting quickly on the threats that matters most.
“The challenge is not collecting data, it is making sense of it and turning it into action.”
From fragmented data to actionable insight
This is where CyberProof’s approach comes in.
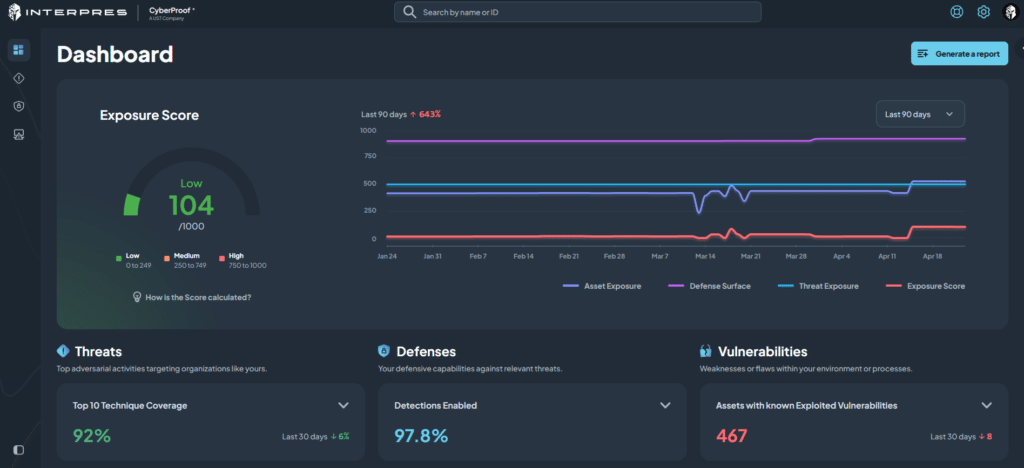
The CDC Reveal360 platform provides centralized cybersecurity visibility into security posture, exposure, and defense performance, enabling data-driven decisions and measurable outcomes, powered by Interpres.
By connecting previously siloed data sources, organizations gain a unified view across active threat campaigns, TTPs, assets, identities, vulnerabilities, endpoints, networks, cloud environments, detections, logging, and security controls.
As Nick puts it, “what’s been missing is the ability to bring everything together, normalize it, correlate it, and present it in a way that clearly shows what needs attention.”
The result is not more data but providing threat-informed meaningful insight into the data you already have. Organizations can clearly identify where gaps exist, what needs to be fixed, and what should be prioritized.
“What’s been missing is the ability to bring everything together and clearly show what needs attention.”
A vendor-agnostic, cross-platform approach
One of the biggest barriers to effective CTEM is vendor fragmentation. Many platforms attempt to unify data, but only within their own ecosystem.
Interpres, and by extension CDC Reveal360, takes a different approach.
Nick emphasizes that “security does not operate in a single-vendor world. To be effective, you need to connect data across all platforms and environments, not just within one ecosystem.”
This vendor-agnostic model allows organizations to maximize existing investments, avoid lock-in, and build a truly integrated CTEM strategy.
AI as an enabler, not a replacement
As AI becomes more embedded in security operations, organizations are increasingly exploring automation at scale. But there is a critical balance to strike.
Nick’s perspective is clear: “automation is essential for scale, but security decisions still require human judgment. Technology should assist analysts, not replace them. We need AI protecting organizations as a counter to AI being used by our adversaries, however, this needs to be done with a human in the loop”
CDC Reveal360 reflects this philosophy. AI is used to enrich, correlate, and prioritize data, while humans remain in control of decisions and actions.
He reinforces this point by noting that “you cannot rely on fully autonomous decisions in complex enterprise environments. Human oversight is critical to ensure accuracy and accountability.”
“Technology should assist analysts, not replace them.”
Making CTEM operational
CTEM is not a single tool, it is a continuous process and methodology.
To make it operational, organizations need:
1) Unified cybersecurity visibility across their environment
2) Context across tools and data sources
3) Prioritization of vulnerabilities, detections, logging and controls, based on real threats
4) A clear path and automation that gets you from insight to action quickly
CDC Reveal360 brings these elements together into a unified operational layer.
By connecting your exposure/attack surface, defensive surface, and threat intelligence, organizations can move from fragmented data to unified insight, and from reactive response to proactive risk reduction.
Final thought
CTEM defines where the industry is heading, but without integration, it remains incomplete.
As Nick summarizes, “the data already exists, and the tools already exist. The challenge is connecting them in a way that drives real, actionable outcomes.” With CDC Reveal360 organizations can finally operationalize CTEM, turning cybersecurity visibility into action and strategy into measurable outcomes.