2026 GLOBAL THREAT INTELLIGENCE REPORT
Mapping Threats and Trends
The CyberProof 2026 Global Threat Intelligence: Mapping Threats and Trends Report provides a comprehensive analysis of the cyber activity that defined 2025, a year marked by the systematic weaponization of identity and the industrialization of AI-driven attacks.
Drawing from internal CyberProof SOC environments, cyber threat intelligence feeds, and broader industry reporting, this document is designed to help Security Operations (SecOps) teams move beyond reactive defense by mapping global threats to emerging trends.

Understanding the Shifting Threat Landscape
Global Cyber Incidents by the Numbers: A Year of Escalation
Defining the 2025 Landscape
Cyber activity in 2025 reflected a decisive shift in how modern intrusions are conducted and scaled. Rather than relying on novel malware or perimeter exploitation alone, threat actors increasingly combined speed, coordination, and identity abuse to turn small access points into high-impact incidents.
The events of 2025 demonstrate that security strategies built primarily around perimeter defense are no longer sufficient. The adversary has moved inside, leveraging the very tools, identities, and supply chains that businesses rely on. As we enter 2026, the ability to validate identity, govern AI usage, and manage third-party risk will determine the difference between a contained incident and a catastrophic breach.
By the end of 2025, identity, cloud, and SaaS environments had become the primary targets, accounting for approximately 22% of all incidents.
Vulnerability exploitation remained a dominant entry vector, with a 17% increase from 2024 comparatively.
Stolen credentials became the top access vector, with 22% of confirmed breaches began with stolen or compromised credentials, the highest of any initial access vector.
80% of retailers faced cyberattacks in 2025, largely driven by identity-centric playbooks.
Key Insights
Mapping Threats & Trends
This comprehensive analysis reveals that 2025 marked a decisive shift in the threat landscape, where malicious actors moved beyond reliance on novel malware to prioritize speed, coordination, and identity abuse, ultimately turning small access points into high-impact incidents across enterprise platforms and SaaS ecosystems. Here are some of the key findings we dive into:
Identity is the New Perimeter
2025 showed a decisive shift away from perimeter bypass and toward identity compromise as the starting point for nearly every major intrusion. High-impact intrusions now routinely begin with attackers operating as legitimate users rather than breaching technical defenses.

The Rise of Ecosystem Threats
The adversary landscape has evolved from isolated groups into collaborative ecosystems. Criminal and state-aligned actors increasingly shared infrastructure, tooling, and access methods, creating blended ecosystems rather than isolated groups.

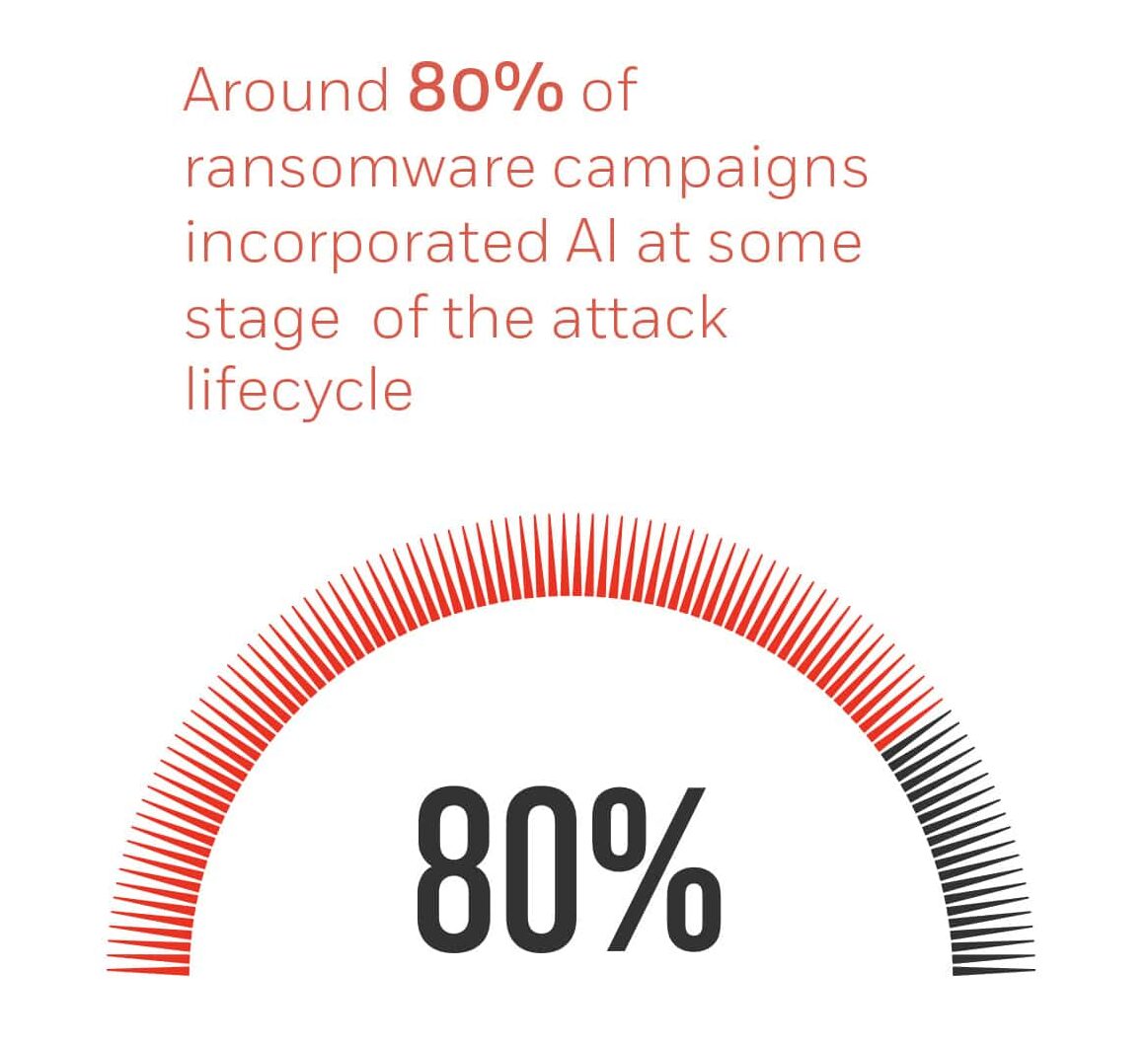
AI-Industrialized Ransomware
AI has transformed the ransomware economy, not by inventing new tactics, but by scaling existing ones at machine speed. AI-enhanced phishing, automated malware generation, and adaptive encryption sharply increased the speed and scale of ransomware attacks.

Platform-Centric & Supply Chain Abuse
Attackers increasingly exploited interconnected SaaS platforms and third-party vendors like IT service providers, MSP tooling, aviation technology suppliers, and even software integrators to reach dozens of downstream victims at once.