Introduction
As organizations reinforce security standards by deploying multi-factor authentication (MFA) across their platforms, cybercriminals are evolving their tactics in response. Rather than simply targeting passwords, attackers are now prioritizing the hijacking of authenticated sessions. One prominent tool emerging in this landscape is Tycoon 2FA, a game-changer that allows adversaries to bypass even robust MFA protections.
Since the first reports surfaced in 2023, Tycoon 2FA has become a central player in cyber incidents targeting organizations using Microsoft 365 and Google Workspace. What distinguishes Tycoon 2FA is not a new malware family, but its sophisticated method of emulating authentic login experiences to intercept sessions in real time.
Let’s dive into what Tycoon 2FA is and how attackers are using it to adapt to stronger security protocols.
What is Tycoon 2FA?
Tycoon 2FA Phish-kit is a phishing-as-a-service (PhaaS) platform used to steal session cookies and bypass two-factor authentication (2FA) protection. The subscription-based toolkit that enables attackers to:
- Replicate Microsoft and Google login pages in real time.
- Intercept credentials, MFA codes, and active session cookies.
- Bypass MFA entirely to impersonate the victim.
- Maintain access well beyond the initial user authentication process.
By employing a reverse proxy, Tycoon phishing kits trick users with legitimate-looking login pages. Every keystroke and authentication response is routed through an attacker-controlled workflow. This Adversary-in-the-Middle (AiTM) approach intercepts traffic between the user and the identity provider, providing the attacker with the data necessary to authenticate as the user, even when MFA is active.
Next, let’s dive into some specific use cases by examining a real-world case study.
Case Study: Identifying an “Impossible Device Shift”
During routine monthly threat hunting activities for clients, the CyberProof Threat Hunting team detected patterns suggesting AiTM activity. Specifically, the team observed an “impossible device shift”. An “impossible device shift” is a cybersecurity threat detection signal indicating a user’s authentication process abruptly jumps between different, geographically separated devices or locations in an unrealistic timeframe. Similar to “impossible travel,” it is a key indicator of “Sneaky 2FA” attacks where attackers use Adversary-in-the-Middle (AiTM) phishing to hijack sessions.
Key Aspects of Impossible Device Shifts:
- Mechanism: An attacker steals a session cookie or intercepts 2FA, causing the security system to see the authentication start on one device (e.g., in a different country) and instantly finish on another, which is physically impossible.
- Detection: Security teams, particularly for Microsoft 365, use KQL (Kusto Query Language) to analyze logs for these discrepancies.
- Context: This technique is used to bypass traditional multifactor authentication by hijacking the session after the user has already approved the request.
This threat is often associated with advanced phishing-as-a-service platforms.
During the aforementioned incident, the following investigation leads were identified within a single authentication flow:
- Two different iOS versions.
- Two different device fingerprints.
- Multiple successful authentications.
All activities tied to the exact same Correlation ID. A Correlation ID is a unique identifier assigned to a single sign-in; under normal circumstances, a single browser and device should be associated with that identifier for the duration of the session. As shown in the investigation logs, this was not the case.
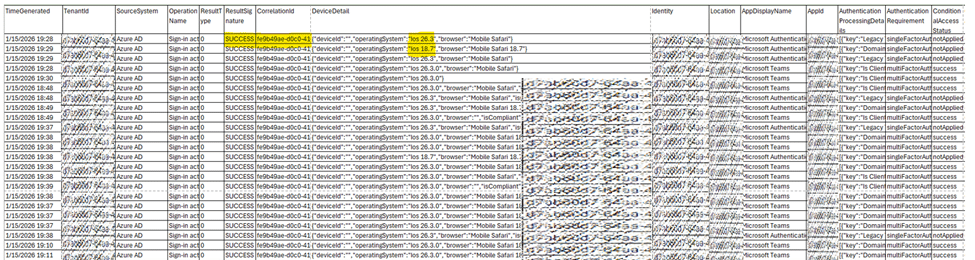
Fig. 1: Same correlation ID seen from our investigation \ios and browser version shifting
Red Flags for Security Analysts
In this example, the same session displayed activity within seconds from:
iOS 18.7: A legitimate user device
AND
iOS 26.3: A non-existent iOS version
Because a single device cannot switch OS versions instantly, this inconsistency strongly suggests:
- User Agent spoofing
- Real-time session takeover
- Simultaneous victim and attacker activity
This behavior is characteristic of AiTM kits like Tycoon 2FA, where the victim logs in normally while the attacker uses a captured session token to authenticate in parallel.
Recommendations
So, what should organizations do to stay ahead of these types of attacks? When indicators of AiTM are detected, immediate action is critical. Consider the following remediation recommendations:
1. Revoke All Active Sessions: Terminate refresh tokens for the affected accounts to invalidate attacker access via the Entra ID portal.
2. Enforce MFA Reset: Set up new MFA authentication method for the issued user in case the existing method captured when the host is compromised.
3. Reset the User’s Password: Resetting credentials eliminates any compromised passwords that an attacker may have obtained.
Threat Hunting Query
To support these recommendations, CyberProof Threat Hunters developed a KQL query to identify single sign-in sessions reporting multiple hardware or browser fingerprints. The logic is straightforward: a user’s Device ID, User Agent, and Operating System should remain consistent during a login session. But if, for example, a session shares a Correlation Id but switches from a managed Windows laptop to a generic Linux machine within the same hour, it warrants investigation.

Conclusion
Tycoon 2FA represents a new generation of identity threats that adapt to multi-factor authentication standards and are difficult to detect. As AiTM platforms become more accessible, organizations must shift their security strategies toward monitoring for inconsistent device fingerprints and abnormal authentication sequences.