Contributors: Niranjan Jayanand, Deepak Nayak, Archana Manoharan
Executive Summary
CyberProof Threat Hunters and Intel Analysts continue to see a new wave of SEO poisoning, that they noticed starting in mid-November 2025, delivering Oyster backdoor tricking users to download malicious office meeting software files like Microsoft teams and Google meet. The samples reviewed were recently compiled and using new infrastructure and difference certificates which were not reported before, however revoked now. We quickly stumbled upon a blog post by Rapid7 researchers in June that shared insights on Oyster backdoor using similar file names but different certificates.
Oyster aka Broomstick aka CleanUpLoader is a family of malware first spotted in September of 2023 by researchers at IBM.
In July 2025, CyberProof Researchers reported on Oyster commonly spreading through malvertising campaigns that impersonate popular IT tools, such as Putty and WinSCP. Several other researchers also reported to news outlets on ransomware groups like Rhysida, that have also utilized this backdoor to target corporate networks.
Technical Details
In September 2025, a Blackpoint SOC reported on a new malvertising and SEO poisoning campaign, threat actors are promoting a fake site that appears when visitors search for “Microsoft Teams download”. In November 2025, a researcher reported on malicious pages through SEO serving Oyster backdoor with file name Google meet.
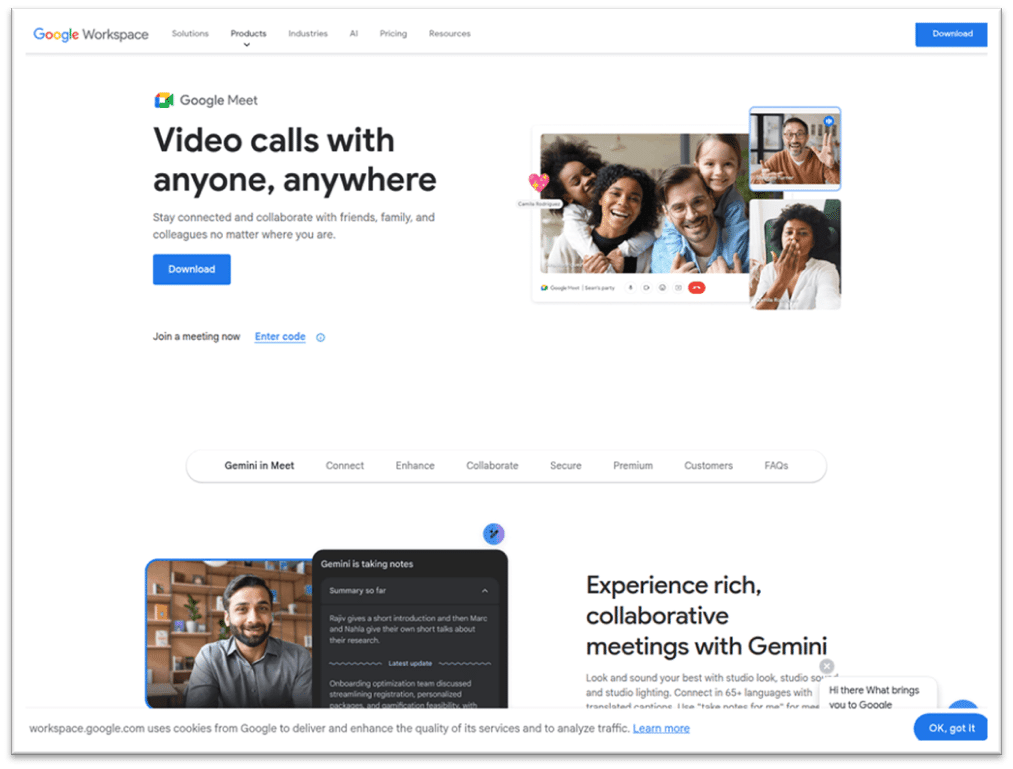
Fig. 1: Image showing malicious page serving Oyster backdoor
Among the sample sets analyzed, the first cluster mimicking MSTeams installer by the name, MSTeamsSetup.exe [VirusTotal] was code-signed with certificates from LES LOGICIELS SYSTAMEX INC. to add legitimacy to the file, mostly revoked now as shown below:
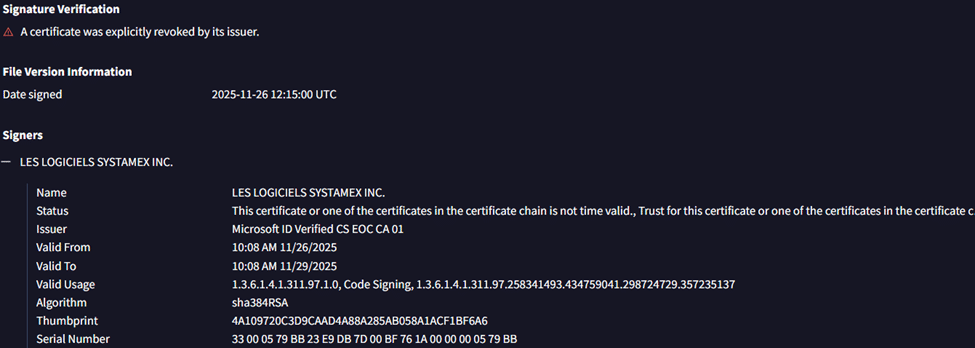
Fig. 2: Revoked certificate details of an executable
Searching VirusTotal for other cluster of files signed by LES LOGICIELS SYSTAMEX INC. showed the following:
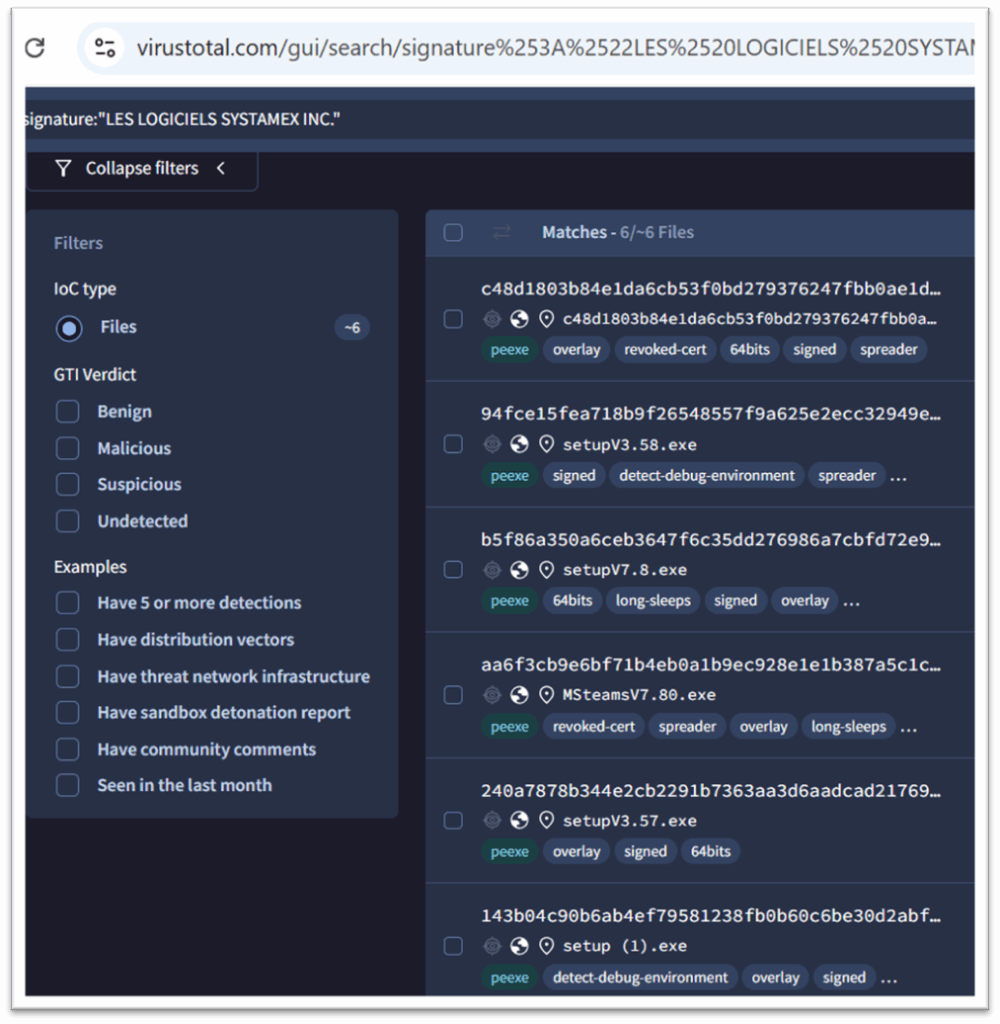
Fig. 3: VirusTotal search for files signed by LES LOGICIELS SYSTAMEX INC.
Searching VirusTotal for other files signed by Reach First Inc. showed the following:
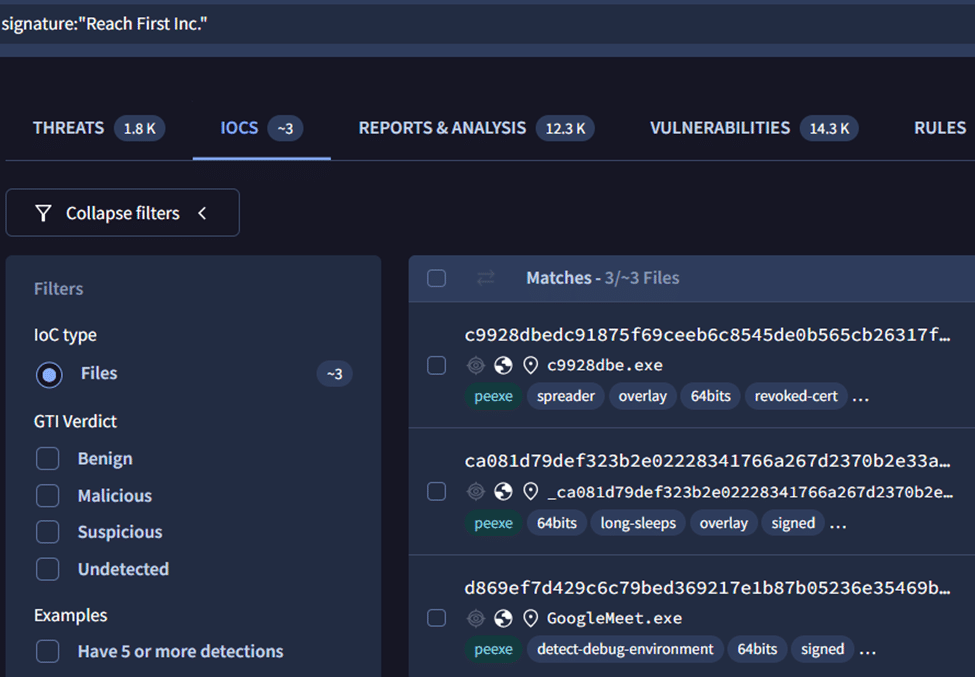
Fig. 4: VirusTotal search for files signed by Reach First Inc.
There was one file signed with S.N. ADVANCED SEWERAGE SOLUTIONS LTD, see below:
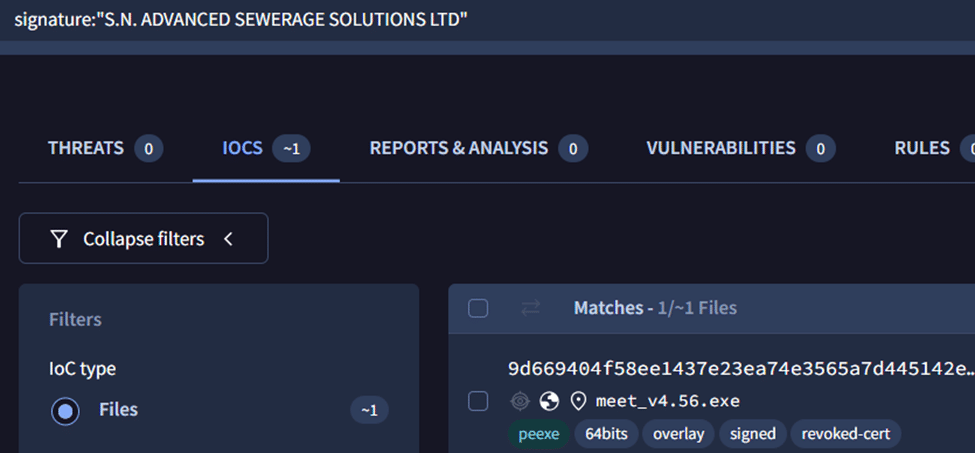
Fig. 5: VirusTotal search for files signed by S.N. ADVANCED SEWERAGE SOLUTIONS LTD
All the reviewed samples, when executed dropped a malicious DLL named AlphaSecurity.dll [triage sandbox link] into the %APPDATA%\Roaming folder. For persistence, the installer creates a scheduled task named “AlphaSecurity” to execute the DLL every 18 minutes, ensuring the backdoor remains active even on reboots.
Indictors of Compromise
File hashes using MSTeamsSetup.exe as file name:
- 383b7fc4a150b448b32c840c300f6986
- b4c3983a720400214202cb02894c9a97
- e9d5e1e8c0adcdf0d2ce66f64b58a73d
- 29148575a488dc05401b6ae11d994aa3
- d960a20a4635f5d300a9b8a9e0ad0998
- c1dd2ca52fff54b8d65d3505d0011c88
File hashes using Googlemeet.exe as file name:
- 3c936de4324a1d1c3e7f5f0219ef881b
- 1bb7ffe095f0a8426b52a01e23f2f882
- 01ddadf71b984fa3e8b68d381fe34ffb
- 8c0255552445edd5d5313f79d732a6f0
Scheduled task:
- “C:\\Windows\\System32\\Tasks\\AlphaSecurity”
Infrastructure domains:
- Tedbutz.com
- Nucleusgate.com
- hxxps[://]www[.]google-meet-app[.]icu/
- hxxps[://]google-meet-app[.]icu/files/meet_v4.56.exe
Conclusion
This malware distribution threat has been active since at least November 2024. Our researchers have observed serveral instances where these attacks use search engine optimization (SEO) techniques and malicious advertising (malvertising) to direct victims to malicious websites that serve malware masquerading as common or popular software. Since there has been some ties with human operated ransomware groups, we strongly believe and predict this threat cluster will continue to be active through 2026.