Contributors: Ian Roth, Head of Product Innovation and Jonathan Maresky, Head of Product Marketing
Enterprise security teams are surrounded by data, but that does not always translate into clarity:
- Threat intelligence sits in one platform.
- Detection coverage lives somewhere else. Vulnerability data is buried in another tool.
- Asset inventory in a CMDB may be incomplete or stale.
- Governance, risk, and compliance reporting often happens in separate workflows entirely.
When leaders ask simple but critical questions such as, “Are we protected against the threats most relevant to us?” or “What value is our security program actually delivering?” the answer often requires manual correlation across disconnected systems. By the time that answer is assembled, it is already out of date.
That challenge becomes even more acute in co-managed environments. Security work is happening continuously, but visibility into that work is often periodic. Clients receive reports and quarterly business reviews, yet they may still lack a continuous, shared view of what is changing across their environment, what the service teams are doing, and what business outcomes are being achieved through those services.
The gap is not effort. The gap is transparency.
CDC Reveal360 was built to close that gap.
With CDC Reveal360, CyberProof introduces a centralized and customizable visibility hub that helps organizations understand not only their security program health, but also the output and value of their managed security services. It brings together threat, defense, exposure, asset, compliance, and operational data into role-specific workspaces that stay current as the environment changes. Instead of forcing teams to stitch together isolated data points, CDC Reveal360 creates a continuous, evidence-based view of security posture and service delivery.
This is not just another dashboard. It is the experience layer where security work becomes visible to the people who need to understand it, in the context they need to act on it.
Problem Statement
Most organizations do not have a shortage of security data. They have a shortage of connected insight.
As enterprise environments expand across cloud, SaaS, on-premises, identities, endpoints, and third-party services, the security stack grows with them. Each tool can answer a narrow question with its own data and specific UI. Few can tell the whole story across a large enterprise:
- Threat intelligence may show which groups are targeting your industry.
- Detection tools may show which alerts fired yesterday.
- Vulnerability platforms may rank exposures by severity.
But leaders still struggle to connect those dots into a single operational narrative: Which threats matter most to our business? Which assets are exposed? Which defenses are in place? Where are our real gaps? What are our teams or service providers doing about them right now? And how do we look from a risk perspective today compared to yesterday or last week?
This fragmentation creates different problems for different stakeholders.
For CISOs and security leaders:
The issue is narrative.
Security posture data lives in multiple systems, so board reporting becomes a manual exercise built from snapshots instead of continuous reality. Leaders are asked to justify investment, prioritize risk reduction, and demonstrate program maturity without a trusted, unified view.
For threat and exposure teams:
The issue is correlation.
Critical intelligence about campaigns, techniques, vulnerabilities, and coverage gaps exists across separate platforms. Analysts spend valuable time exporting, remapping, and rebuilding context rather than focusing on decisions and action.
For security operations managers:
The issue is operational context.
Team workload, service-level agreement status, alert handling, and analyst throughput are often measured separately from the threat landscape those teams are defending against. That makes it harder to understand whether operations are aligned to actual risk.
For service delivery leaders and client security owners:
The issue is transparency.
Value is delivered continuously, but visibility is periodic. When the only meaningful update comes during the next review meeting, managed security can feel like a black box. That creates unnecessary friction in the partnership and makes it harder for internal security leaders to communicate progress upward.
For compliance leaders:
The issue is proof.
Checkbox reporting is no longer enough. They need current evidence that controls, posture, and remediation efforts are aligned with ongoing requirements.
In short, the problem is not capability. It is visibility. Security leaders need a way to turn fragmented activity into a continuous, shared understanding of posture, performance, and value.
Solution
CDC Reveal360 addresses this problem by creating a centralized visibility hub built around how security actually works, catering to workflows that are most relevant to each persona.
CDC Reveal360 unifies data from across the security ecosystem into configurable, persona-aligned workspaces. These workspaces can incorporate cyber threat intelligence, defense telemetry, detection coverage, vulnerabilities, assets, identities, governance, risk and compliance data, and security operations center performance metrics. That means stakeholders no longer have to piece together multiple disconnected views just to understand what is happening.
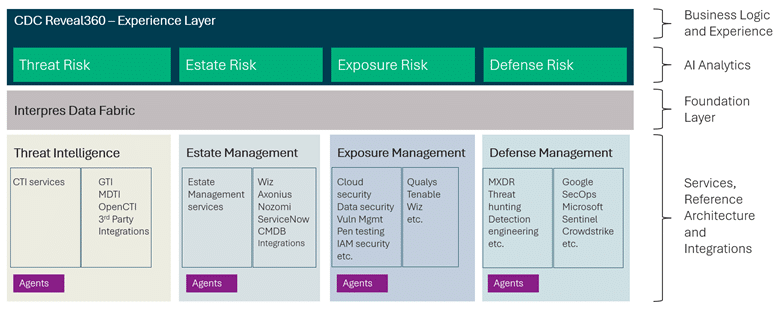
CyberProof’s platform architecture
The platform is powered by CyberProof’s broader platform architecture, which includes Interpres as the data foundation. Interpres connects four critical domains: threat, estate, exposure, and defense. It maps relationships across threat actors, campaigns, techniques, assets, vulnerabilities, identities, detections, and controls, allowing organizations to move beyond isolated tool outputs and toward connected analysis. CDC Reveal360 then turns that connected analysis into collaborative, role-based workspaces where both CyberProof teams and client teams can see the same reality in real time.
That matters because security decisions rarely happen inside a single tool. They happen across teams:
- A CISO may need a board-ready view of posture trends, service outcomes, and investment priorities.
- A threat analyst may need to understand which MITRE ATT&CK techniques used by active adversaries lack detection coverage.
- A security operations manager may need to compare ticket volume, SLA health, and analyst throughput against real exposure levels.
- A compliance leader may need centralized monitoring that ties reporting back to live controls and operational evidence.
CDC Reveal360 supports these distinct needs without forcing everyone into the same generic interface.
Just as important, CDC Reveal360 helps teams move from awareness to action without losing context. Users can start with a high-level summary, drill into coverage maps or risk-based metrics, and pivot into the appropriate underlying tool when action is required. Instead of producing static reports that quickly expire, CDC Reveal360 creates persistent, evolving views that remain useful between quarterly reviews, executive updates, and audit cycles.
For CyberProof’s managed services clients, this becomes the shared surface between client teams and CyberProof teams. Service delivery is no longer hidden behind tickets and slide decks. Clients can see detections added, alerts triaged, posture shifts, integration status, and operational outcomes as they happen.
Transparency becomes continuous rather than episodic.
Picture a QBR, but with graphs and KPIs that you can create immediately and continuously.
Business value and benefits
The business value becomes clearer when viewed through the lens of the people who use it.
For CISOs and security leaders, CDC Reveal360 helps turn security posture into business language. Instead of manually assembling point-in-time updates, they gain persistent access to unified posture trends, exposure prioritization, service outcomes, and board-ready metrics. That supports faster risk decisions, clearer justification of security investments, and stronger communication with executives, boards, and regulators. It also helps demonstrate program maturity with evidence, not assumptions.
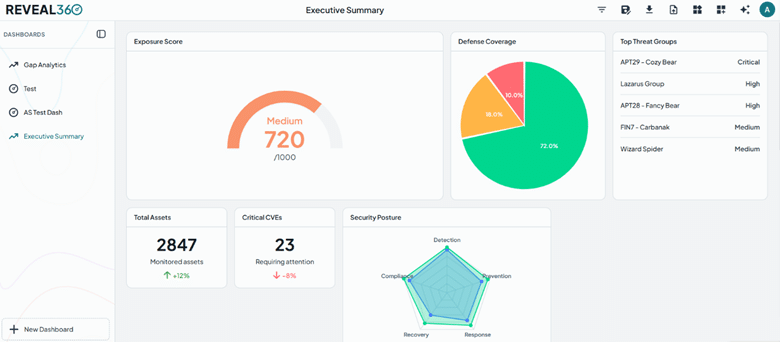
Example CDC Reveal360 executive summary dashboard
For threat management analysts and exposure teams, CDC Reveal360 reduces the friction of manual correlation. By layering threat intelligence, campaigns, ATT&CK coverage, exposure data, and defense gaps into a single analytical surface, analysts can focus on what matters most: identifying where real adversary behavior intersects with real weaknesses. That leads to better prioritization and more defensible decisions about where to tune detections, remediate vulnerabilities, or expand coverage.
For security operations managers, CDC Reveal360 connects performance with risk. Rather than looking at SOC metrics in isolation, they can view workload distribution, SLA status, alert throughput, and operational health alongside the threat and exposure context their teams are working against. That makes it easier to manage capacity, improve response quality, and align operational effort to the areas of greatest risk.
For service delivery managers and client security leads, CDC Reveal360 creates a more transparent managed service relationship. It provides a live view of what is being done, what has improved, what still needs attention, and how service activity maps to business outcomes. That helps internal security leaders communicate value upward without becoming full-time report builders, and it helps managed service partnerships feel measurable, collaborative, and continuously accountable.
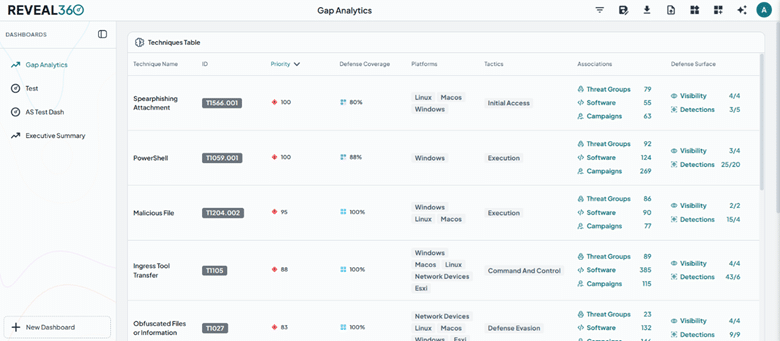
Example CDC Reveal360 gap analysis view
For compliance and risk leaders, CDC Reveal360 provides centralized monitoring and tracking that goes beyond checklist reporting. It helps connect compliance posture to actual operational data, making it easier to track progress, support audits, and show how security activity contributes to risk reduction in practice.
These benefits are consistent with what CyberProof has already helped clients achieve across broader engagements:
- In one retail and healthcare case study, a threat-informed assessment surfaced high-priority MITRE techniques with weak detection coverage and identified vulnerabilities tied to relevant adversary activity, helping the client shift toward more intelligent prioritization.
- In a manufacturing environment, CyberProof’s platform-led approach improved visibility across IT and OT while contributing to faster detection and response.
- In pharmaceutical environments, clients gained stronger visibility, reporting, automation, and operational collaboration.
CDC Reveal360 builds on that same platform-first, outcome-focused approach by making those results continuously visible.
Ultimately, the business value is straightforward: better visibility leads to better decisions. Better decisions lead to better prioritization, stronger performance, clearer accountability, and more credible communication with the business.
Summary
Security teams do not need more disconnected views. They need a way to understand how everything connects.
CDC Reveal360 gives organizations a centralized, continuous view of security posture, service performance, and operational outcomes. By unifying fragmented data into persona-specific workspaces, it helps leaders see the health of their security program, understand the value their managed services are delivering, and take action with context intact.
In a world where threats move continuously and stakeholders expect evidence, not assumptions, visibility cannot depend on the next quarterly presentation. It has to be available all the time.
That is the promise of CDC Reveal360: continuous clarity for the people responsible for protecting the business.
Next steps
See CDC Reveal360 in action at RSAC and discover how it can help your organization connect posture, performance, and business value in one shared experience.
Register for the launch webinar and see Ian Roth, CyberProof Head of Product Innovation, explain the rationale behind CDC Reveal360 and demo popular use cases.
Request a demo to explore how role-configured workspaces can bring together your threat, exposure, defense, asset, compliance, and SOC data into a single, continuously updated view.
Or take your own self-guided tour of CDC Reveal360.
Talk with CyberProof about how CDC Reveal360 can support your priorities as a CISO, security operations leader, compliance owner, or managed service stakeholder.
And if you are evaluating how to modernize visibility across your environment, ask CyberProof about starting with a threat exposure assessment to identify gaps, prioritize what matters most, and define the right next step for your security program.
CDC Reveal360 is available as a standalone platform through Microsoft Azure Marketplace and Google Cloud Marketplace and is also included as part of CyberProof managed service offerings.